by Max Sullivan, Web Developer and Beth Bridges, V.P. of Digital Identity
Don’t Let Your Hacked Website Become a Cybercriminal’s Tool
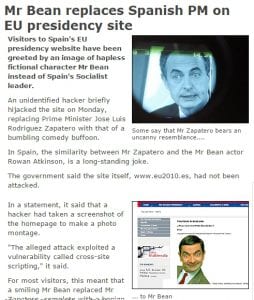
Do you think of website hacking as something like digital graffiti? It’s the online equivalent of someone spray-painting the high school marquee to say “Home of the Losers.” For example, in 2010, the Spanish Prime Minister’s website popped up a picture of Mr. Bean for search results.
Not all web defacements are so innocent, some offer threats or disturbing images, and at the very least are literal vandalism of another person or organization’s property.
Random Cameos are The Least of the Threats
 But there are far worse types of hacks and unless you know where to look, you’ll never see it. The first sign might be when Google interdicts your site, serving up the scary “The site ahead contains malware” screen to your visitors before they get to see your site.
But there are far worse types of hacks and unless you know where to look, you’ll never see it. The first sign might be when Google interdicts your site, serving up the scary “The site ahead contains malware” screen to your visitors before they get to see your site.
Then it’s an 8-step process to remove the problem, clean up your site, andrequest Google review your site to remove this warning. It may take days orweeks. In the meantime, no one wants to visit your site.
It gets worse. There are hacks that don’t trigger Google’s malware or virus warnings. Instead, they suck up your hosting space, corrupt your files, andruin your SEO rankings.
[Editor’s Note: Websites are not just hacked for the financial benefit of the hackers, but also for political activism. The group “Anonymous” has been on a campaign of DDoS attacks against extremist websites (DDoS = distributed denial of service) as well as finding and reporting their social media accounts to shut them down. They’ve recently announced increased effortsagainst ISIS in response to the Paris bombings and attacks. The new wars are increasingly moving to the cyber realm.]
 Spam Hacking is Not Delicious or Nutritious
Spam Hacking is Not Delicious or Nutritious
It’s a money-making scheme. A spammer will find a vulnerability in your hosting site or in your website code. Then, they’ll use automated software to create hundreds or thousands of random pages stuffed with keywords to try to get them to show up in search results.
These pages will link into sites that are full of ads. They make pennies when someone clicks. Or, the pages are full of affiliate linksto file download sites, where again, the hacker makes a bit of money for each file that’s downloaded.
It may be pennies, but these hackers have automated the process. It works day and night seeking out sites that are vulnerable. Once it’s in, if left to run rampant, it will create thousands of pages “courtesy” of your hosting account.
If you’re paying for your hosting based on bandwidth (i.e. the number of visits and the size of the files served up from your site), it could be costing you money. Or the spam pages may suck up the available bandwidth, making your site unbearably slow for legitimate visitors.
Poison Links for Your Site
Most of these hackers aren’t trying to save puppies. They generate these pages to sell warez (illegal software copies), porn, and medications like Viagra and Cialis. These are not a few of Google’s favorite things and certainly nothing that you want your digital identity to be associated with. And yet… because these pages are created on your site, your domain is now associated with these terms for your Search Engine Optimization.
For example, you have legitimate pages like www.YourSite.com/about-our-company. But this hack also generates hundreds of pages like www.YourSite.com/viagra-cialis-cheap-medications. Five pages about your legitimate activities and 995 about cheap or illegal prescriptions. What do you think Google thinks your site is all about?
These links are “poison.” A key component of any successful SEO campaign is to have high-quality links pointing to and from your site. Until this kind of hack is cleaned up and prevented, your SEO efforts, no matter how good, will be wasted.
 Keeping Zombies Away from Your Site
Keeping Zombies Away from Your Site
Your website needs to be constantly updated, maintained, and checked. If you or your web developer haven’t looked at your site in months, stale content could be the least of your worries.
Your web designer or developer should be looking at your site regularly to check for spam, hacks, and simple broken bits of code. They should also be checking for and updating components, plugins, modules, and extensions whenever there’s an update – not just for function, but for security.
You or someone on your team needs to check in once every while to see what’s going on and make sure your site looks good. It’s an added benefit of constantly adding new content and applying security updates; you and your website developer, designer, and content marketer will be looking at your site, both the front and backend.
A website that is built, left alone, and on its own not only looks outdated but probably doesn’t accurately reflect your current business. It’s also vulnerable to these hacking attacks.
The longer your site sits there abandoned, the more uninterrupted time these hackers have to find and exploityour website.
The solution? Ongoing maintenance in addition to content development. There could be zombies lurking there, working hard for someone else’s profit.
Mr. Bean/Mr. Zapatero courtesy of http://news.bbc.co.uk/2/hi/8440554.stm
Anonymous collage courtesy of CC BY-SA HonestReporting.com
Zombie Minion photo by James O’Gorman via Creative Commons license CC BY-SA 4.0
Use of photos or descriptions of actions do not constitute any endorsement of illegal cyber activities.


VIEW ALL